IN THE MIDDLE OF TYPING THIS AND HERE IS WHAT THEY DID
Note I was working typing they remote access, attack erased much of what I typed, you can see they erased entire sections and left partial incomplete sentences and portions removed, to keep me from saying that the old machines being attacked not because they did not work, but because of their upgrades and alterations it will not work.
2010 and before machines were working fine, the keys were working, but the new system was not secure, the cloud, so to force the newer ZSK KSK verisign keys, they want ALL machines to have similar systems, so they can force their administration and control one long continuous chain of connection so they can constantly stream, and send updates to other machines, but mostly for gaming, and streaming of films and television shows, the only way it works to stream the music is to have the ability to send the packets of info constantly to update it all.
They want the ability to connect to the "cloud" which is not some remote server farm but rather all of our computers they hijack and take over control of.
They want to defraud us of the use of the machines they sold us, and then use them for their purposes, their business interests. They want all of the actual operating systems gone, as that data takes up space, and they think, clearing it, erasing it all, to leave nothing but a shell and a non working browser interface that we will all just accept it.
Even machines the companies now sell they stopped making updates for and they as they are are exactly this "shell" of an interface designed to go to the cloud.
A cloud that not everyone wants or will use. So to force use, they erase word office programs, defrauding people who had it and never had a need to buy any other, they as companies get the idea if they ERASE IT then we have to REPURCHASE IT renting access to it on the cloud, and they MICROSOFT , GOOGLE APPLE and all of them will let you rent space and use of their cloud which is the complete and total connection of our computers as a larger super network all so they can control it and stream through it so as to make them money by taking up our hard drive space. Space we can not use for our files, because of course our files are in the way! SO they think solution is to REMOVE FILES to their "cloud" and doing so it frees up all the space for them to PUSH DATA THROUGH updates , gaming, video streaming so we can collectively use the web.
Their grand design works, ONLY if you and I and everyone CONSENTS!
BUT DID YOU? DID I? NO!
They did NOT ASK CONSENT BEFORE VIOLATING US ALL!
At NO point did they do this ever!
Now you might say the people buying new computers know, but do they?
Do they realize that Apple MacBook Air is sold and has NO UPDATES and is being made OBSELETE? So should they sell it NO! NOT when they won't support it!
Microsoft does the SAME THING, with Windows 10, did you ask to change it?
OR DID YOU BUY IT?
Did you think it would have email, and office and wordpad and notepad and all the essential things? YES, but DID YOU THINK MICROSOFT WOULD ERASE IT ALL, not BEFORE, BUT AFTER THEY SOLD IT TO YOU?
They DID!
They now, ERASE IT, Windows Essentials, from machines, and REMOVE IT, with NO CONSENT OF THE OWNER, why to make us use CLOUD BASED APPS!
BUT WHY? Because they WANT TO SELL OUR DATA!
They make 500 MILLION PLUS a year doing just that, selling EMAIL INFO and DATA from APPS, and the APPS on the system REMOTE ACCESS AT RANDOM, TURN ON WEBCAM AND AUDIO to RECORD, YES RECORD YOU! AT HOME in the so -called "privacy" or is it, of your home!
For so-called "marketing" or product research ADOBE owned jointly by all the tech companies, will USE YOUR WEBCAM WITH NO CONSENT AND TAKE AUDIO AND VIDEO! APPS like, facebook APPS do so, browser APPLE APPS, WINDOWS STORE MICROSOFT APPS all do so! THEY SELL YOUR DATA!
Pictures, profile info, EVERY WORD YOU TYPE AND SAY, ALEXXA, SIRI and CORTANA and GOOGLE MUSIC STATIONS APPLE MUSIC STATIONS all of YOUR PHONES you walk around with, the AI is RECORDING!
You may have MAY HAVE AGREED, but DID ANYONE AROUND YOU?
In your HOMES, in your OFFICES, in business and legal and health appointments?
It is NOT the only APP doing so!
NOW, the WHOLE WINDOWS SYSTEM AND BROWSER IS AN APP and they all do so, the component parts are "APPS" and they ALL take your PRIVATE DATA!
They SELL IT!
While in the middle of your most private conversations or what you wrote in emails, it is taken.
TRY to OPPOSE them and STAY on an OLD SYSTEM OR COMPUTER to AVOID IT THE VIOLATIONS!
You might say that would be SMART!
IT IS, UNTIL THEY REALIZE people would do so!
THAT would foil their plans to move EVERYONE to CLOUD.
SO to make ALL OLD computers rendered useless, they have to have a WAY to MAKE US SWITCH OR UPGRADE AND BUY NEW!
BECAUSE through ANTI TRUST ACTION, they ALL have now got stock and ownership stake and JOINT BUSINESS INTERESTS, think Microsoft and APPLE, or GOOGLE and SPOTIFY, MICROSOFT AND BELL, and ROGERS AND YAHOO, now ALL of them want to SELL your data.
TO GET IT, they MERGE, then they REMOVE EMAILS, and limit file uploads, UNDER UNITED NATIONS CHARTER no GOVERNMENT and or BUSINESS can interfere with communications, BUT NOW THEY DO!
YOU ARE BEING FORCED to USE their CLOUDS if you want DATA transfers, you can NOT just add files to emails anymore can you? NO you need to use their cloud service or emails are stopped, APPS delete emails, destroy evidence in court cases, they do not care, they erase data to FREE UP SPACE on YOUR SYSTEM, because THEY not you CONTROL IT!
They, want to stream gaming data, to do so, or to update the neighbours windows security updates they want to PUSH DATA THROUGH ALL OF OUR COMPUTERS in a CHAIN one by one.
Connecting EVERYONE is NOT SECURE, we KNOW THIS!
In 8 lines of DOS or less emails, that NEVER USED TO BE PASSWORDS, but NOW Microsoft FORCES YOU TO DO SO, and to have REMOTE ACCESS,
you nor I consented to it, but they need it, to make a CHAIN of one ADMINISTRATION to CONTROL ACCESS through FORCE and AGAINST CONSENT, so NOW you can NOT CHOOSE a sensible password, NO they FORCE through upgrade it to be your email. THEN anyone with it can remote access.
CAN YOU STOP IT?NO!
When PASSWORDS were secure, then there was SOME security, NOW NO!
Medical Health RECORDS accessed by hackers, WHY because they computer systems , are altered, to have EMAILS as PASSWORDS< in 8 lines of DOS on systems where WiFi can NOT be removed then a person in the vicinity CAN OBTAIN AND ACCESS ANY OTHER COMPUTER!
Is ANY computer safe, NO! NOT with this assinine system!
BUT does Government do anything to stop it? NO!
The CORRUPT CRIMINAL POLITICIANS, like Justin Trudeau do actual PUBLICITY FOR THE MICROSOFT COMPANY AND MELINDA GATES CHARITY WHILE IN OFFICE, and SUPPOSED TO BE ACTING AS PRIME MINISTER, but is he, NO he TRUDEAU COMMITTED ETHICS VIOLATIONS!
And when he is TOLD HOW AND WHY systems are being attacked and WHEN CANADIAN GOVERNMENT SYSTEMS HAVE BEEN ATTACKED WHY IT IS HAPPENING DOES HE DO ANYTHING? NO!
ALL HE DID WAS PROMOTE THE CRIMINAL OFFENDERS DOING AND CAUSING IT TO HAPPEN!
2018 Canada's TAX SYSTEM IS NOW COMPROMISED.
THEY SENT WRONG INFO DUE TO HACKING THAT HAS OCCURRED!
The Windows systems, even when the Government was TOLD that data from court cases and evidence and system wide data was being erased it did nothing to stop microsoft though they were given cease and desist and still Microsoft accessed machines and destroyed programs files and evidence in court cases.
Microsoft knew it would be sued then to go further it ERASED ALL PROGRAMS FILES EVIDENCE AND EVEN WRITING SOFTWARE TO OBSTRUCT JUSTICE
Canadian Government was complicit in their actions WORSE as it benefitted them NOW TRUDEAU AND MORNEAU WANT TO STAND IN PARLIAMENT AND TRY TO TAKE TAX DOLLARS TO GIVE NOT TO THE CITIZENS THAT NEED SERVICES BUT TO TECH COMPANY EXECUTIVES FOREIGNERS AND MULTI BILLION DOLLAR CEO COMPANIES OUR TAX DOLLARS FOR AI ARTIFICIALL INTELLIGENCE PROGRAMS> TAXES ARE NOT LEGALLY ALLOWED TO GO TO PRIVATE BUSINESS NOR DONARS TO CAMPAIGNS! #ETHICSVIOLATIONS It is CRIMINAL what they are doing to ALL of us now!
The criminality of Canada's Government is outrageous!
I was typing then they knocked me offline to more windows stop code errors and reboot then i got back on hit browser then restore pages got it back to blog and it had saved while typing so now i hit publish as is to document it all they still either microsoft or government are now attacking to continue to obstruct justice . feb 26 th 2018 stressed and ptsd getting worse by their actions.
They keep trying to keep me from typing this, to explain WHY the OLD MACHINES and OPERATING SYSTEMS that were working NOW DO NOT, as the OTHER blog post from verisign I saved EXPLAINS WHAT they are doing it and WHY trying to CONNECT A CHAIN in a LARGER way IS A MASSIVE PROBLEM, it caused the USD to retry then back to TCP if the DNS servers and IPS can not be recognized THEN ALL OLD SYSTEMS and SERVERS are NOW NOT ABLE TO CONNECT TO THE NET OR SEE WEBSITES!
THAT IS 10% or more roughly 80 MILLION PLUS PEOPLE AFFECTED OR MORE! ALL with machines or sytems BEFORE 2010
WILL THEY EXPLAIN THIS TO PEOPLE? NO!
THEY HIDE IT ALL BECAUSE THEY CAUSE IT!
The computers WERE SECURE and ARE if they ARE NOT connected to the cloud or the CHAINS under their ADMIN FORCED AGAINST PEOPLES WILL!
If the old systems were left and the verisign used all the old keys and the operating systems had the PREVIOUS AND PROPER LOG IN SECURITY then our systems would be SECURE and FILES AND DATA SECURE!
BUT NOW, they CHANGE IT both system and KEYS without consent at anytime either Verisign or Microsoft feels like it and we have NO CHOICE? THAT IS ILLEGAL FOR THEM TO DO THIS TO US!
VIOLATION OF CHARTER RIGHTS!
ALSO companies like EXPERION charging you money to see if your data is on the dark web, WELL IT WOULD NOT BE THERE IN THE FIRST PLACE IF GOOGLE FACEBOOK APPLE AND MICROSOFT HAD NOT SOLD IT TO ANY AND EVERYONE CAUSING THE HARM TO ALL IN THE FIRST PLACE NOW WOULD IT?
THIS VIOLATION OF ALL OF US HAS TO STOP NOW!
THEY DELIBERATELY SLOW AND THROTTLE OLDER SYSTEMS WHY BECAUSE THEY CAN NOT ALTER IT TO THE NEW KEY SYSTEM UNTIL EVERYONE IS SWITCHED OVER! NOT ALL WILL AGREE TO SWITCH> IF THEY DO NOT THEY CAN NOT ACCESS THE WEB> THAT DEFRAUDS THEM ALL!
TECH COMPANIES WANT THE NEW KEYS FOR SECURITY OF CLOUD AND CHAIN CONTROL OF SYSTEMS THEY CANT MAKE IT SECURE TO CONNECT UNTIL IT IS SWITCHED. SO REALITY THEY CAN NOT LEGALLY MAKE PEOPLE SWITCH WHICH STOPS THEM IN THEIR TRACKS SO THEY ALL START ATTACKING USERS OF OLD SYSTEMS THROUGH SHEER FORCE TO MAKE THEM DO SO THAT IS CRIMINAL! THEY THE CEOS NEED TO BE PROSECUTED NOW FOR HARMING BUSINESS EDUCATION AND LIFE OBSTRUCTING JUSTICE IN COURT CASES BECAUSE THE DELIBERATE DESTRUCTION OF PROPERTY IS CRIMINAL MISCHIEF UNDER CRIMINAL CODE AND KNOWING DEFRAUDING PEOPLE IS ANOTHER AMONG MANY CRIMES BOTH CRIMINAL AND CIVIL ACTION NEEDS TO BE TAKEN NOW!
IF ANYONE TRIES THEY SABOTAGE THEM SO THEY CAN NOT TYPE NO PROGRAMS ARE LEFT TO EVEN DO THAT TRYING TO GET ONLINE TO TYPE THEY ATTACK! DATA ERASED EMAILS ERASED EVIDENCE DELETED BY THEM ALL OBSTRUCTION OF JUSTICE!
INCREASING THE STRENGTH OF THE ZONE SIGNING KEY FOR THE ROOT ZONE
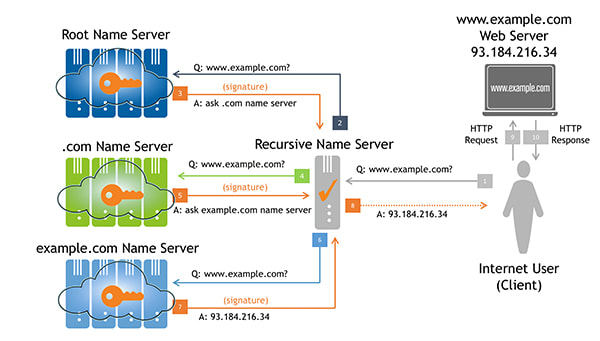
One of the most interesting and important changes to the internet’s domain name system (DNS) has been the introduction of the DNS Security Extensions (DNSSEC). These protocol extensions are designed to provide origin authentication for DNS data. In other words, when DNS data is digitally signed using DNSSEC, authenticity can be validated and any modifications detected.
A major milestone was achieved in mid-2010 when Verisign and the Internet Corporation for Assigned Names and Numbers (ICANN), in cooperation with the U.S. Department of Commerce, successfully deployed DNSSEC for the root zone. Following that point in time, it became possible for DNS resolvers and applications to validate signed DNS records using a single root zone trust anchor.
DNSSEC works by forming a chain-of-trust between the root (i.e., the aforementioned trust anchor) and a leaf node. If every node between the root and the leaf is properly signed, the leaf data is validated. However, as is generally the case with digital (and even physical) security, the chain is only as strong as its weakest link.
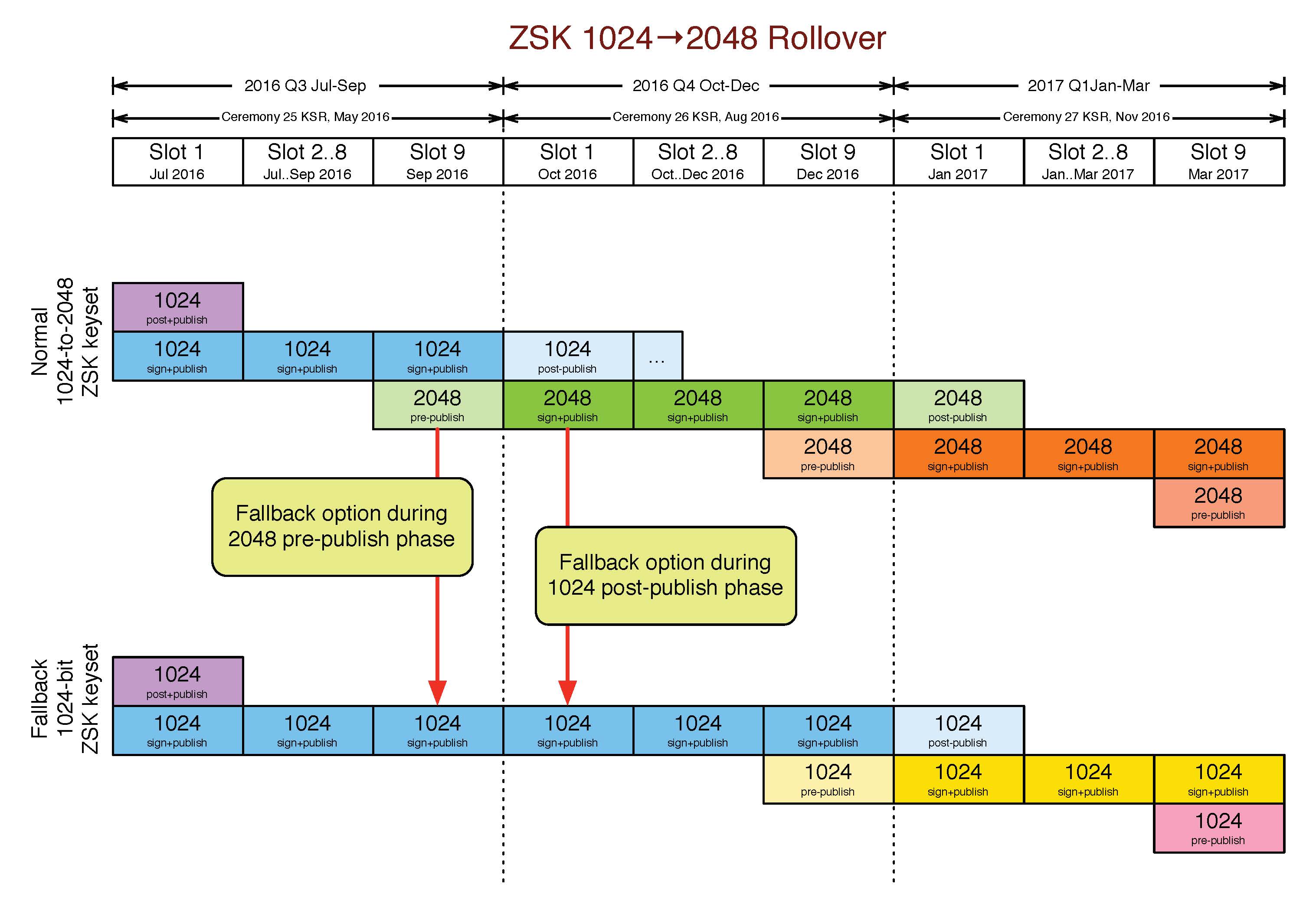
To strengthen the chain at the top of the DNS, Verisign is working to increase the strength of the root zone’s Zone Signing Key (ZSK), which is currently 1024-bit RSA, and will sign the root zone with 2048-bit RSA keys beginning Oct. 1, 2016.
With this change, the root zone ZSK size will match the size of the KSK: both will be 2048-bits. One difference, however, is that the ZSK is changed (rolled) four times per year, or approximately every 90 days.
The root zone will not be the first to use a 2048-bit ZSK. Approximately 60 top-level domains (TLDs) are known to be using 2048-bit RSA ZSKs already.
Verisign, in its role as the Root Zone Maintainer and root zone ZSK operator, is actively involved in communication and cooperation with other relevant groups and partners, including: ICANN, the U.S. Department of Commerce, the root server operators, and the larger communities of DNS operators and internet users. In 2015, Verisign publicly presented research on the effects of increasing the ZSK. More recently we shared our plan and schedule at the 24th DNS-OARC Workshop in Buenos Aires.
WHY YOU SHOULD CARE
An increase in the size of the root zone ZSK leads to an increase in the size of DNS responses from the root name servers. As DNS responses become larger, we worry more and more about the ability of root server clients to receive them. Sometimes large DNS responses have difficulty reaching their destinations due to IP fragmentation. It is well-known that many types of internet firewalls, routers and middleboxes block IP fragments. Clients behind such devices might never receive fragmented User Datagram Protocol (UDP) DNS responses. They’ll be forced to retry with lower UDP Payload Size values, or perhaps over Transmission Control Protocol (TCP).
Note that even if your recursive name server is not configured for DNSSEC validation, it might be configured to receive DNSSEC signatures. Many name server implementations are configured, by default, to ask for the DNSSEC data with each response.
For the upcoming increase in ZSK size, all normally-occurring DNS responses are still well below the typical size at which fragmentation must happen for Ethernet interfaces: 1472 bytes. With a 2048-bit ZSK, responses exceeding 1300 bytes will rarely be seen. [1]
Nonetheless, it is important to ensure that internet users are able to receive larger responses when they are seen, including signatures from 2048-bit ZSKs. To that end Verisign has developed a web-based utility that anyone can use to test their network and name server’s ability to receive larger, signed responses.
TEST YOUR NETWORK
Visit keysizetest.verisignlabs.com to perform the test. The page will load a small image file in the background from a number of subdomains, each signed with different ZSK and KSK parameters. The results are displayed on a table, and a successful test should look like this:
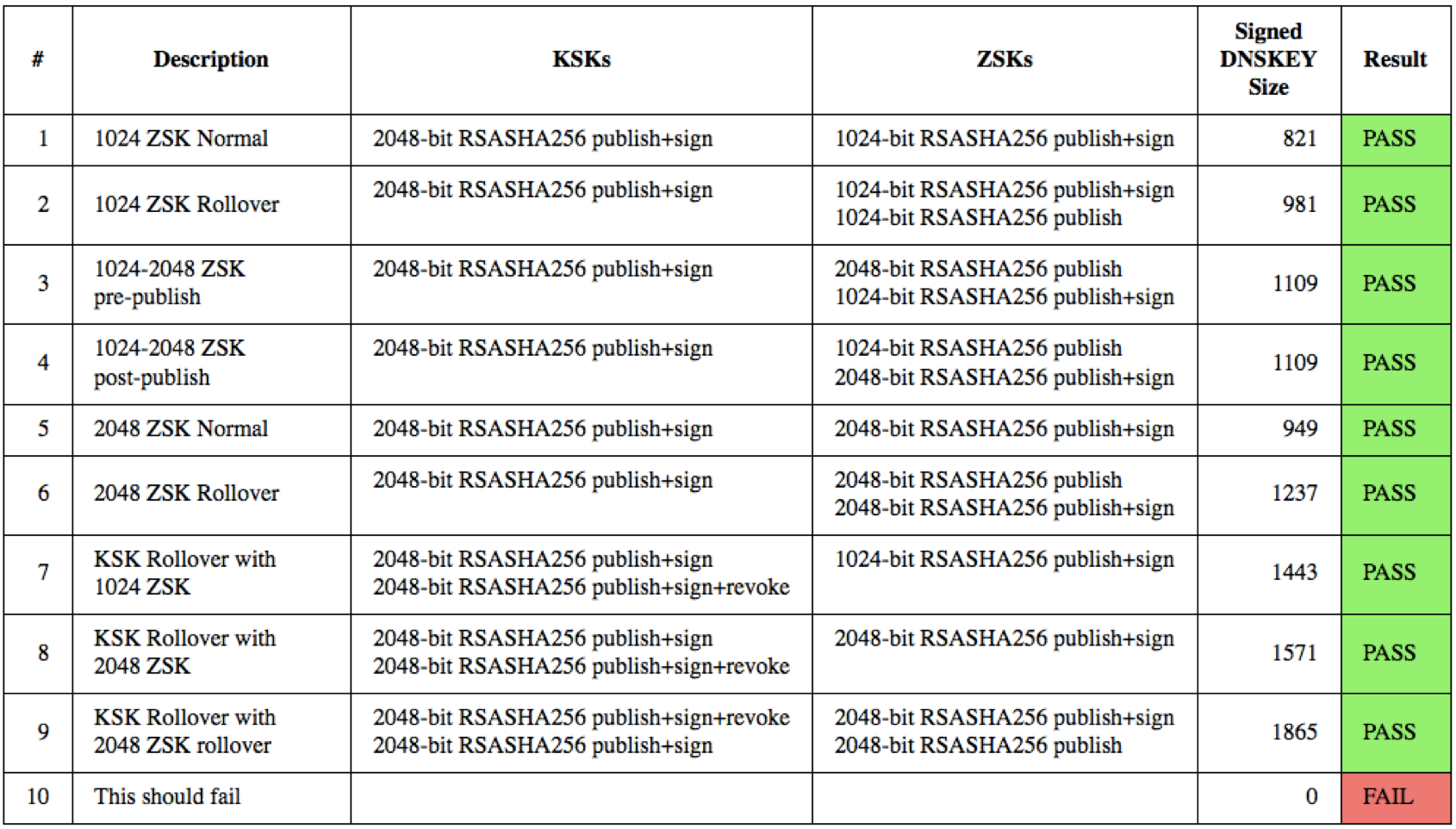
If you see different results, you should investigate as described on the web page. If you seem unable to solve problems related to resolution of domains signed with large DNSSEC keys, send an email to Verisign at info@verisign-grs.com.
DEPLOYMENT SCHEDULE
Both Verisign and ICANN have already spent a significant amount of time on development and testing of their systems to support 2048-bit ZSKs. As part of this process, Verisign has upgraded the Hardware Security Modules (HSMs) used to store private keys and to generate signatures from them. The next steps are:
- Mid-May: ICANN to sign the transitional ZSKs at its next key signing ceremony.
- Sept. 20: The first 2048-bit ZSK will be pre-published in the root zone. This follows the normal process for quarterly ZSK rollovers whereby incoming ZSKs are pre-published for a period of approximately 10 days. Should any unforeseen problems arise during this time, Verisign has the ability to “unpublish” the new ZSK and continue using the old one.
- Oct. 1: Verisign will publish the first root zone signed with a 2048-bit ZSK. The outgoing 1024-bit ZSK will remain in a post-publish state for approximately 30 days. Similarly, should any unforeseen problems arise during this time, Verisign has the ability to revert to signing with the previous 1024-bit ZSK.
Please take a few moments to test your systems by visiting keysizetest.verisignlabs.com. If you have any concerns that you’d like to make Verisign aware of, please contact us at info@verisign-grs.com.
1. Exceptions being responses to the SOA and ANY query types.







